Evidence Management System: Core Features, and How to Choose One
By Nisha Bangeja on April 27, 2026, ref:
Every criminal case in the United States now generates digital evidence. Body-worn cameras, surveillance systems, interview recordings, mobile device extractions, drone footage: the volume grows each year, and most agencies still lack a centralized way to handle it. A 2024 Police Executive Research Forum (PERF) survey found that 67% of law enforcement agencies have no unified digital evidence repository. Files sit on DVDs, thumb drives, shared network folders, and individual workstations. Evidence gets lost. Chain of custody breaks. Cases collapse.
An evidence management system (EMS) is a centralized platform that ingests, stores, organizes, secures, and shares digital evidence across its entire lifecycle. For police evidence management, the right EMS replaces scattered physical media with a single auditable repository that maintains chain of custody from collection through courtroom presentation and final disposition.
This guide covers what an evidence management system actually does, which capabilities separate adequate platforms from effective ones, and how to evaluate whether a system meets your agency's compliance and operational requirements.
Key Takeaways
- An evidence management system centralizes digital evidence from all sources into one auditable, tamper-evident repository with unbroken chain of custody.
- CJIS compliance, AES-256 encryption, and SHA-256 tamper detection are baseline requirements for any law enforcement evidence platform.
- Agencies should evaluate deployment flexibility (cloud, on-premises, hybrid) because data sovereignty requirements vary by jurisdiction and agency type.
- AI capabilities like transcription, redaction, and object detection reduce manual evidence review time from hours to minutes per file.
- Multi-portal architecture enables secure evidence sharing with prosecutors, defense attorneys, and courts without compromising internal investigation segregation.
What Is an Evidence Management System and Why Does It Matter?
An evidence management system is software that handles the full lifecycle of digital evidence: ingestion from cameras and devices, secure storage with encryption, organization by case and folder, AI-assisted processing, controlled sharing with authorized parties, retention policy enforcement, and lawful disposition. It functions as the digital equivalent of a physical evidence room, with one critical advantage: audit trails that record every access, every download, and every modification automatically.
The need is urgent. The Bureau of Justice Assistance (BJA) estimates that the average U.S. law enforcement agency now manages between 2 and 10 terabytes of digital evidence annually. Larger metro departments handle far more. Without a purpose-built system, agencies face three critical risks:
-
Evidence spoliation: Files stored on portable media degrade, get overwritten, or simply go missing. A single lost USB drive can make key footage inadmissible.
-
Chain of custody gaps: When evidence passes through email, file shares, or physical handoffs, there's no verifiable record of who accessed what and when. Understanding what happens when the chain of custody breaks shows why this risk is not theoretical.
-
Compliance failures: Federal standards like CJIS and state-level regulations (California AB-748, Texas SB1) impose specific handling, encryption, and retention requirements that manual processes can't consistently meet. For a deeper look at these obligations, see this guide on compliance for evidence handling.
An EMS eliminates these risks by enforcing security policies, logging every interaction, and automating retention schedules at the platform level.
Which Core Features Should Every Evidence Management System Include?
Not all systems are equal. Some platforms started as generic cloud storage and bolted on evidence features later. Others were built from the ground up for criminal justice workflows. When evaluating platforms, these capabilities separate functional systems from inadequate ones.
Centralized ingestion from multiple sources
The system should accept evidence from body-worn cameras, dash cameras, CCTV systems, interview room recordings, drones, mobile devices, and third-party platforms. Vendor-agnostic ingestion is critical. If your EMS only works with one camera manufacturer's files, you're trading one silo for another.
Look for watch folder capabilities that automatically ingest files from monitored network directories, bulk upload tools for large evidence batches, and mobile apps that let officers upload from the field.
Multi-format support
Evidence arrives in dozens of formats: MP4, AVI, WAV, JPEG, PDF, proprietary camera formats, and more. The platform should handle 200+ file formats natively without requiring manual conversion. Converting files introduces integrity questions that defense attorneys will exploit.
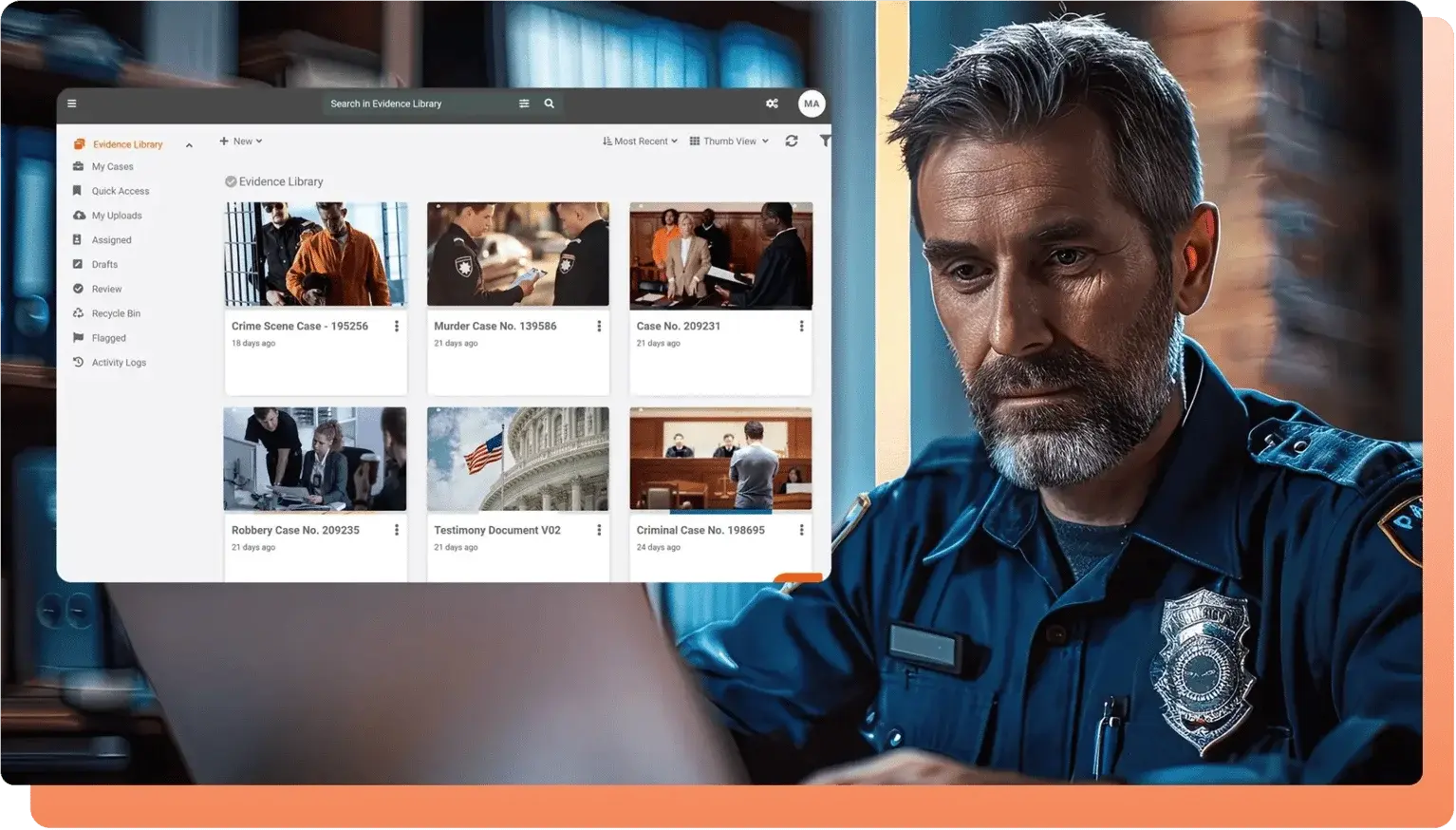
Case and folder organization
Evidence should be organized hierarchically by case, with folders, tags, and metadata that make retrieval fast. When a detective needs to find all body camera footage from a specific incident, they shouldn't spend 30 minutes digging through file trees.
Retention and disposition management
Different evidence types have different retention requirements. Homicide evidence may need indefinite retention. Misdemeanor footage might have a 3-year window. The system should enforce configurable retention policies automatically, including legal holds that prevent deletion of evidence tied to active cases. Disposition workflows should align with NARA (National Archives and Records Administration) standards.
Why Does Chain of Custody Make or Break Evidence Admissibility?
Chain of custody is the documented, unbroken record of every person who handled a piece of evidence and every action taken on it. Courts require this documentation to verify that evidence hasn't been tampered with, altered, or substituted between collection and presentation. One gap in the chain is all a defense attorney needs to challenge admissibility.
In a digital context, chain of custody means the system automatically logs:
- Who uploaded the evidence, when, and from what device or source
- Every view, download, share, annotation, and export with timestamps and IP addresses
- Any modifications, redactions, or processing applied to the file
- Hash values (SHA-256) computed at ingestion and verified on demand to detect tampering
These audit logs must be immutable. If an administrator can edit or delete log entries, the entire chain becomes questionable. WORM (Write Once, Read Many) storage for audit logs prevents this. For more on how digital audit trails protect evidence integrity, see this detailed breakdown.
The strongest platforms generate exportable chain-of-custody reports as PDF or CSV files that prosecutors can submit directly to the court. This eliminates the manual documentation that has historically been one of the weakest links in evidence handling.
How Do Compliance Standards Shape Evidence System Requirements?
Agencies don't get to choose whether to comply with evidence handling standards. The standards are mandatory, and the penalties for non-compliance range from audit findings to evidence exclusion to federal funding loss. These are the frameworks that most directly affect evidence management system selection. For a practical look at how these controls work in day-to-day operations, see this guide on CJIS compliance in digital evidence management.
CJIS Security Policy
The FBI's Criminal Justice Information Services (CJIS) Security Policy governs any system that stores, processes, or transmits criminal justice information. Requirements include AES-256 encryption at rest, encryption in transit, multi-factor authentication, role-based access controls, and detailed audit logging. Any evidence management system used by law enforcement must support CJIS-compliant deployments.
FIPS 140-2
Federal agencies and many state agencies require cryptographic modules validated under FIPS 140-2. This isn't about using encryption; it's about using validated encryption implementations. If your system runs on infrastructure with FIPS-validated modules (like Azure Government Cloud), this requirement is typically met at the infrastructure layer.
FedRAMP
Federal agencies deploying cloud-based evidence systems need FedRAMP authorization at the Moderate or High impact level. FedRAMP High is required for law enforcement and criminal justice data. Agencies should verify whether the vendor holds FedRAMP authorization directly or achieves compliance through a FedRAMP-authorized hosting provider.
State-specific mandates
California's AB-748 requires release of body-worn camera footage within 45 days for certain incidents. Texas SB1 imposes specific BWC retention and access rules. Georgia's Open Records Act creates disclosure obligations. Your evidence system must support configurable policies that accommodate your state's requirements, not just federal standards.
What Role Does AI Play in Modern Evidence Processing?
The volume of digital evidence has outpaced the capacity of human reviewers. A single body camera generates 8 to 12 hours of footage per shift. Multiply that across an agency with 200 officers, and you're looking at 2,400 hours of video per day. No team can review that manually. AI doesn't replace human judgment, but it drastically cuts the time investigators spend searching for relevant content. For a broader look at how AI is transforming this space, see 12 ways to boost efficiency with AI in evidence management.
Automatic transcription and translation
Speech-to-text processing converts audio and video evidence into searchable text. An investigator searching for a suspect's name or a specific phrase can find it across thousands of hours of recordings in seconds instead of days. Multi-language support matters in diverse communities. Leading platforms support 50 or more languages with published accuracy benchmarks, so agencies can verify transcription quality before trusting results.
Object and face detection
AI models can identify and tag people, vehicles, license plates, weapons, and other objects within video footage. This turns unstructured video into searchable, indexed evidence. Object tracking follows detected items throughout the entire video, so reviewers can jump directly to relevant segments without scrubbing through hours of footage.
Automated redaction
Before releasing evidence under FOIA or public records requests, agencies must redact personally identifiable information (PII): faces of bystanders, license plates, addresses visible on screen, and spoken PII in audio. Manual redaction of a single one-hour video can take 4 to 8 hours. AI-powered redaction reduces this to minutes by automatically detecting and masking PII across visual and audio channels simultaneously.
Evidence summarization
Long-form recordings from interviews, depositions, or surveillance can be summarized by AI to extract key points. This helps investigators prioritize which evidence to review in full and which can be scanned at the summary level.
How Should Agencies Evaluate Deployment Options?
Deployment model is one of the most consequential decisions in evidence system selection. It affects data sovereignty, compliance posture, operational cost, and long-term flexibility. There's no single right answer. The right model depends on your agency's regulatory environment and IT infrastructure.
Cloud (SaaS)
Cloud deployment offers fast setup, automatic updates, and no on-site hardware maintenance. For agencies without large IT teams, SaaS is often the most practical option. The critical question is which cloud. Standard commercial cloud may not meet CJIS or FedRAMP requirements. Government cloud environments (like Azure Government) provide the compliance certifications that law enforcement needs. For smaller agencies evaluating this path, this guide on CJIS-compliant cloud evidence management covers the key considerations.
On-Premises
Agencies handling classified evidence or operating in air-gapped environments (common in federal law enforcement and intelligence) may need on-premises deployment. This gives complete control over data location and network access but requires dedicated IT staff for maintenance, patching, and scaling.
Hybrid
Many agencies are transitioning from legacy on-premises systems to cloud. Hybrid deployment lets them maintain existing infrastructure while gradually migrating to cloud storage. This is also useful for agencies that need certain evidence categories (classified, sensitive) to remain on-premises while routine evidence moves to the cloud.
The key evaluation criterion: does the vendor support all three models, or are you locked into one? Agencies that choose a cloud-only vendor today may face a painful migration if data sovereignty requirements change tomorrow.
Why Does Multi-Agency Evidence Sharing Require Portal Architecture?
Evidence doesn't stay within one agency. Prosecutors need access to police evidence. Defense attorneys have discovery rights. Courts need exhibits. Internal affairs investigations require strict segregation from standard evidence. Federal task forces involve multiple agencies sharing evidence across jurisdictions.
A flat permission model, where everyone sits in one system with different roles, can't handle this complexity safely. Portal-based architecture creates separate, isolated workspaces for each stakeholder group. Each portal has its own security policies, access controls, and user management. Evidence can be shared between portals through controlled, audited channels without exposing one group's data to another.
This architecture supports scenarios like:
-
Law enforcement portal: Primary evidence repository with full access for authorized officers and evidence custodians.
-
Prosecution portal: Prosecutors see only evidence shared with them for specific cases, with time-limited access links.
-
Internal affairs portal: Completely segregated from the main evidence repository, with independent administrator controls.
-
Community evidence portal: Secure upload channel for civilians to submit evidence (tips, witness video, surveillance footage).
Without portal-level segregation, a permissions misconfiguration could expose internal affairs investigation footage to patrol officers or give defense attorneys access to evidence not yet disclosed through discovery.
How VIDIZMO DEMS Addresses These Requirements
VIDIZMO DEMS supports CJIS-compliant deployments on Azure Government Cloud, on-premises for air-gapped environments, and hybrid configurations.
The platform ingests evidence from any body-worn camera manufacturer, dash cameras, CCTV, interview rooms, drones, and mobile devices, handling 255+ file formats without conversion. SHA-256 tamper detection and WORM-enabled audit logs maintain chain of custody from ingestion through disposition.
AI capabilities include transcription in 82 languages, automated redaction, object detection and tracking, speaker diarization, and evidence summarization. Multi-portal architecture provides separate, security-isolated workspaces for law enforcement, prosecutors, defense, internal affairs, and community evidence submission.
If your agency is evaluating how to modernize evidence storage and management, start with the evaluation checklist above. Map your requirements to the capabilities that matter most for your jurisdiction, evidence volume, and compliance obligations.
Request a free DEMS trial to see how the platform handles your agency's specific evidence workflows.
Evidence System Evaluation Checklist
Use this framework when comparing platforms. These criteria reflect the operational and compliance realities discussed above.

People Also Ask
An evidence management system is a centralized software platform that handles the full lifecycle of digital evidence, including secure ingestion, encrypted storage, case-based organization, AI-assisted processing, controlled sharing, retention policy enforcement, and lawful disposition. These systems maintain chain of custody through immutable audit logs and cryptographic hash verification, ensuring evidence remains admissible in court.
At minimum, law enforcement evidence management systems must support CJIS Security Policy compliance, which requires AES-256 encryption at rest, encryption in transit, multi-factor authentication, role-based access controls, and audit logging. Federal agencies also need FedRAMP authorization (Moderate or High). State-specific mandates like California AB-748 and Texas SB1 impose additional BWC-specific requirements.
The system automatically records every interaction with evidence: uploads, views, downloads, shares, annotations, exports, and modifications. Each action is logged with the user's identity, IP address, timestamp, and event details. SHA-256 hash values computed at ingestion detect any tampering. Audit logs stored in WORM (Write Once, Read Many) storage cannot be edited or deleted, ensuring the chain remains unbroken from collection through courtroom presentation.
VIDIZMO DEMS differentiates on three fronts: deployment flexibility (SaaS, government cloud, on-premises, hybrid, and air-gapped environments), AI breadth (transcription in 82 languages, automated redaction, object detection, and the CaseBot natural-language investigation assistant), and multi-portal architecture that enables secure evidence segregation for law enforcement, prosecution, defense, internal affairs, and community portals within a single platform.
Vendor-agnostic systems can ingest footage from any body-worn camera brand, including Axon, Motorola, Panasonic, and others, without requiring proprietary connectors. This prevents hardware lock-in and lets agencies standardize evidence management even when different departments use different camera equipment. VIDIZMO DEMS supports 255+ file formats and automated ingestion through watch folders and bulk upload.
AI automates the most time-consuming evidence processing tasks. Automatic transcription converts audio and video into searchable text, enabling keyword searches across thousands of hours of recordings. Object detection tags people, vehicles, and weapons within footage for instant retrieval. Automated redaction of faces, license plates, and spoken PII reduces FOIA processing from hours per video to minutes. Evidence summarization extracts key points from long recordings so investigators can prioritize full reviews.
Start Evaluating Your Evidence Management System
Selecting an evidence management system is one of the most consequential technology decisions a law enforcement agency makes. The right platform protects evidence integrity, accelerates investigations, meets compliance mandates, and enables secure collaboration across the justice ecosystem. The wrong one creates new risks.
About the Author
Nisha Bangeja
Nisha Bangeja is a Product Marketing Executive at VIDIZMO covering AI-driven video and evidence management technology. She focuses on how public safety agencies and enterprise teams can leverage emerging innovations to drive measurable operational impact.
Jump to
You May Also Like
These Related Stories
Police Evidence Management: 10 Features That Protect Cases & Save Time

Key Features of Effective Digital Evidence Management Systems




No Comments Yet
Let us know what you think