How to Prevent Digital Evidence Tampering and Ensure Integrity
By Wasif Baig on April 30, 2026, ref:
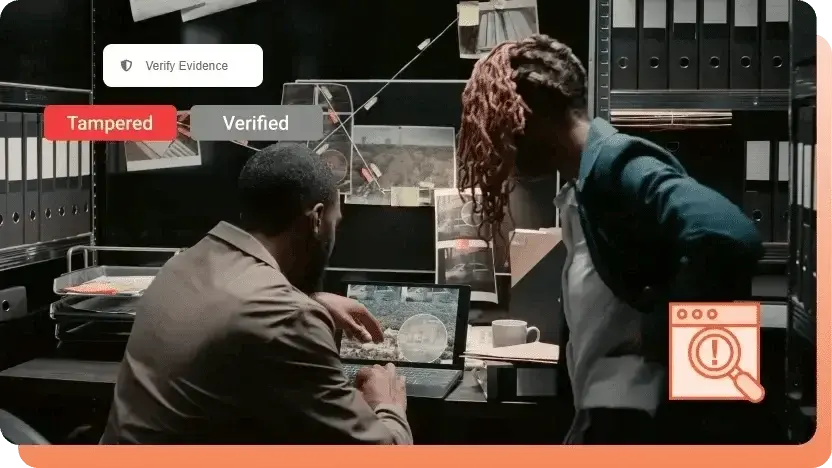
Imagine a high-profile criminal trial where a piece of evidence is crucial to the case, such as a surveillance video showing the defendant at the crime scene. Now imagine that the integrity of that video is in doubt. The footage could have been manipulated, altered, or fabricated. The consequences of that kind of breach are catastrophic. This is digital evidence tampering, and it is one of the fastest ways to undermine an otherwise sound case.
Evidence today rarely arrives as paper or physical objects. It is video from a smartphone, audio from a recorded call, electronic documents, body-worn camera footage, or images shared across multiple agencies. As digital files have become indispensable to investigations and audits, the same properties that make them powerful also make them vulnerable. Files can be edited, metadata rewritten, copies multiplied, and traces of access erased.
Tampering with a physical object like a bloody knife is far harder than altering metadata on a digital file. Depending on the sophistication of the person manipulating the evidence, digital alterations can be effectively undetectable. From a legal and regulatory perspective, intent matters less than provability. If an organization cannot demonstrate that evidence has remained unchanged from the moment of capture, that evidence becomes vulnerable to challenge or exclusion regardless of what it actually shows.
This article covers why evidence integrity is foundational to the justice system, what happens when tampering occurs, what federal and state law say about it, the seven red flags that indicate evidence has been compromised, and the practical safeguards that prevent it.
Why Evidence Integrity Matters
Maintaining evidence integrity is fundamental to the justice system. It ensures that every legal investigation and court proceeding is based on accurate, reliable, and unaltered information, and it directly determines whether legal outcomes are fair.
In court, evidence is what establishes guilt or innocence. When that evidence has been tampered with or its integrity is in question, it can be ruled inadmissible. The consequences extend in every direction. An innocent person can be wrongfully convicted. A guilty person can walk free because the evidence against them has been excluded. The prosecution can lose its case before it begins, because the foundation of any legal argument is the credibility of the evidence behind it. Charges can be dismissed, convictions can be overturned, and entire investigations can collapse.
Beyond individual cases, compromised evidence damages the broader criminal justice system. When agencies cannot demonstrate that they handle evidence reliably, public trust in law enforcement erodes. Communities cooperate less. Cases take longer to resolve. The cost is paid not just by the parties involved but by everyone who depends on a justice system that works.
Consequences of Digital Evidence Tampering
When evidence is tampered with, the fallout reaches well beyond the case in question.
Inadmissibility of Evidence in Court
Tampering breaks the chain of custody. The chain of custody is the documented log of every person who handled or shared the evidence and under what conditions, from the moment of collection to the moment it is presented in court. If someone accessed the evidence without authorization, the chain of custody captures it, including the time and any changes that were made.
Once tampering is identified, the evidence can no longer be trusted to represent what it originally captured. Courts respond accordingly: tainted evidence is excluded, and the case built on it is weakened or dismissed.
Legal Consequences for Digital Evidence Tampering
Tampering itself is a crime, intentional or otherwise. Federal law and the Federal Rules of Evidence treat it seriously. Charges can include obstruction of justice, computer crime, perjury, and destruction of evidence. The severity of the penalty depends on the nature of the evidence, the intent behind the tampering, and the jurisdiction.
Tampering can be classified as a misdemeanor or a felony depending on state law and the specific act. Courts may impose up to one year in jail for misdemeanors, and longer prison terms plus fines for felonies. Federal charges can carry up to 20 years. Prior criminal history typically results in harsher sentences.
Wrongful Convictions and Unjust Acquittals
Tampered evidence increases the risk of both wrongful convictions and unjust acquittals. When key evidence is compromised, its reliability becomes the central issue of the case rather than what the evidence shows.
Doubt about authenticity can result in acquittals that do not reflect the actual facts, or in lesser charges that fail to match the severity of the offense. At the same time, fabricated or planted evidence can put innocent people at risk of being wrongly convicted.
Disruption of Ongoing Investigations
Evidence tampering misleads investigators. Altered or destroyed evidence creates false leads, sends teams down incorrect paths, and consumes time and resources that could have been spent solving the case. Strong cases become weak ones. Weak cases collapse. Suspects evade capture. Active investigations stall while teams reconstruct what should have been preserved in the first place.
Damaged Public Trust
When tampering becomes public, it does not just damage the case in question. It damages the institution. Communities that perceive corruption, incompetence, or bias in how evidence is handled lose confidence in law enforcement and the courts. That loss of trust translates directly into reduced cooperation, fewer reported crimes, and a harder time prosecuting the cases that do come forward.
What Federal and State Law Say About Tampering
Evidence tampering is addressed under both federal and state law, and the specific statutes vary in scope and severity. A few of the most cited examples:
Federal Law
The federal obstruction of justice statute, 18 U.S.C. § 1519, prohibits anyone from corruptly altering, destroying, or concealing a record or tangible object with the intent to influence a federal investigation. Penalties include fines and a prison term of up to 20 years.
Georgia Law
Georgia law, § 16-10-94, treats tampering with evidence as a felony when the underlying matter is a felony case, with prison terms ranging from 1 to 3 years. For cases involving serious violent felonies, the sentence can be between 1 and 10 years. Tampering associated with misdemeanors is itself classified as a misdemeanor.
California Law
Under California Penal Code § 141, tampering with evidence covers knowingly and willfully altering, modifying, planting, or concealing physical matter, digital images, or video recordings with intent to obstruct justice or misrepresent evidence.
For general cases this is a misdemeanor. When a peace officer commits these acts with specific intent to mislead or destroy evidence, it becomes a felony punishable by 2 to 5 years in state prison. Prosecuting attorneys who intentionally alter or withhold material evidence in bad faith face felony charges as well, with penalties of 16 months to 3 years.
7 Red Flags That Indicate Digital Evidence Tampering
Spotting tampering is as important as preventing it. None of these red flags proves evidence has been altered on its own, but each one weakens your ability to prove integrity, and that burden of proof falls on whoever holds the evidence.
1. Inconsistent or Altered Metadata
Metadata records when a file was created, modified, and accessed, and which device captured it. The earliest sign of tampering is usually metadata that does not match the known facts of an incident: timestamps that conflict with reported timelines, missing device identifiers, or stripped geolocation data. Inconsistencies alone do not prove tampering, but they invite scrutiny of everything else about the file.
2. Broken Chain of Custody Records
A verifiable chain of custody documents every interaction with evidence from collection to presentation. Gaps in custody, manually maintained or editable logs, and undocumented transfers are immediate warning signs. Courts weigh chain of custody heavily; if it cannot be demonstrated clearly, the evidence is likely to be challenged regardless of what it shows.
3. Evidence Modified Without Documentation
Even routine actions like exporting, converting, or enhancing a file can count as tampering if they are not properly recorded. Files altered without documented reasons, no record of when or why changes were made, and an inability to distinguish the original from modified versions all compromise authenticity. Intent does not factor in much here. Any unexplained change undermines the file.
4. Unexplained Changes in File Format or Resolution
Changes in format, resolution, bitrate, or compression suggest a file has been re-encoded after collection. Native footage converted to a compressed format, resolution or frame rate changes without documentation, and audio quality degradation are common examples. Re-encoding happens during legitimate sharing too, but undocumented changes make it impossible to prove the content was not altered in the process.
5. Missing or Incomplete Audit Logs
Audit logs show how evidence is accessed and handled. When logs are disabled, stored separately from the evidence, or fail to capture viewing, downloading, or sharing activity, accountability collapses. Without reliable logs, there is no way to know whether evidence was accessed or modified without authorization.
6. Unauthorized Access or Permission Changes
Insider risk is often the bigger threat. Unexpected permission changes, evidence accessed by people without a clear role-based need, and shared credentials are the typical signals. The more people who can access evidence, the higher the risk of accidental or intentional modification.
7. Evidence Stored Outside a Secure System
Local drives, USB devices, shared folders, and unsecured cloud storage all lack the basics: encryption, automated chain of custody, and immutable audit logs. Evidence stored this way is harder to defend in court and accounts for a disproportionate share of admissibility challenges.
Any single red flag is enough to raise questions in court. Several together all but guarantee the evidence will be challenged. The goal is not to react when these signs appear, but to design evidence handling so they cannot appear in the first place.
How to Prevent Digital Evidence Tampering
Effective prevention closes the gaps that produce the red flags above. Four practices form the foundation.
Chain of Custody Documentation
A well-documented chain of custody is the single most important safeguard for evidence integrity. It is a chronological record of who possessed the evidence, when, and for what purpose, from collection through final presentation in court.
A rigorous, automated chain of custody does two things at once: it deters tampering by making every action traceable, and it provides the proof of authenticity courts expect. Manual logs introduce gaps and editability that compromise both, which is why purpose-built systems generate custody records automatically.
Proper Handling and Secure Storage
Evidence has historically lived on loose media like USB drives, DVDs, and external hard disks. These devices are vulnerable to mishandling, theft, physical damage, and unauthorized access, and every transfer is a manual handoff that creates a fresh gap in custody.
Centralized digital evidence storage solves this. Files are encrypted at rest and in transit, protecting against unauthorized access, preventing undetected modification, and creating a clear audit trail. Moving off loose media and onto a secure system eliminates an entire category of risk while making evidence easier to retrieve and share when it is actually needed.
Robust Access Controls
Access controls determine who can view, modify, or share evidence, and they need to operate at two layers.
The first layer protects the platform. Multi-factor authentication adds a second proof of identity beyond the password. Role-based permissions restrict access by job function, so an analyst sees only what an analyst should see. Location-based restrictions can block access from regions outside jurisdictional boundaries.
The second layer protects specific files. Requiring a documented justification before viewing sensitive evidence creates accountability for every access event. Strong identity, role-based scope, and per-file accountability are what close the unauthorized-access red flag in practice.
Implement Tamper Detection Measures
Even with strong access controls, organizations need a way to verify that a file has not changed since collection. Tamper detection provides that verification cryptographically.
When a file is uploaded, the system generates a unique hash from its content, like a digital fingerprint. Any change to the file, however small, produces a different hash. To verify integrity, the system regenerates the hash from the current file and compares it to the original. A match confirms the file is unchanged; a mismatch flags it as tampered.
Tamper detection backed by Secure Hash Algorithm cryptography is what lets organizations prove integrity rather than just claim it. Combined with chain of custody, secure storage, and access controls, it gives evidence the defensibility courts expect.
Key Takeaways
- Evidence integrity is the foundation of fair legal outcomes. Compromised evidence leads to wrongful convictions, dismissed cases, and lasting damage to public trust in the justice system.
- Seven red flags reveal tampering: inconsistent metadata, broken chain of custody, undocumented modifications, unexplained format or resolution changes, missing audit logs, unauthorized access, and evidence stored outside a secure system.
- Tampering carries serious legal penalties. Federal obstruction charges under 18 U.S.C. § 1519 can carry up to 20 years in prison, and state laws range from misdemeanors to felonies depending on jurisdiction and intent.
- Prevention rests on four practices: documented chain of custody, encrypted secure storage, robust access controls with multi-factor authentication and role-based permissions, and cryptographic tamper detection.
- Provability is the common thread. Courts do not just want evidence to be unaltered; they want the holder to be able to prove it. Systems that generate that proof automatically are the ones that hold up under scrutiny.
Protect Evidence Integrity with VIDIZMO Digital Evidence Management System
Evidence tampering leads to wrongful convictions, failed prosecutions, and eroded public trust. Preventing it requires technology built for evidence security from the ground up.
VIDIZMO Digital Evidence Management System (DEMS) offers automated chain of custody reporting, built-in tamper detection, granular access controls with multi-factor authentication, and CJIS-compliant security. Replace vulnerable loose media with a centralized repository and accelerate case resolution using AI-powered search across spoken words, faces, and metadata.
Trusted by the California DMV, Georgia Attorney General's Office, and county governments nationwide.
People Also Ask
Digital evidence tampering is the unauthorized modification, deletion, falsification, or destruction of digital files used as evidence. It can be deliberate or unintentional, but in either case it compromises the file's authenticity and legal admissibility.
Evidence integrity ensures that legal decisions are based on accurate, reliable information. Without it, courts cannot rule fairly, the wrong people may be convicted or acquitted, and public trust in the justice system erodes.
The seven most common red flags are inconsistent or altered metadata, gaps in the chain of custody, undocumented file modifications, unexplained changes in format or resolution, missing audit logs, unauthorized access or permission changes, and evidence stored outside a secure system.
Detection methods include metadata analysis to spot timeline inconsistencies, cryptographic hash verification to confirm files have not changed, audit log review to trace access activity, and chain of custody review to identify gaps or unauthorized transfers.
Penalties depend on jurisdiction and the nature of the underlying case. Federal obstruction charges under 18 U.S.C. § 1519 can carry up to 20 years in prison. State laws range from misdemeanors with limited jail time to felony charges with multi-year sentences, particularly when tampering involves law enforcement officers or prosecutors.
A hash is a unique cryptographic fingerprint generated from a file's contents. If even a single bit of the file changes, the hash changes too. By comparing the current hash of a file to the one captured at the time of collection, organizations can prove with mathematical certainty whether the file has been altered.
The most effective prevention combines a strict chain of custody, encrypted secure storage, robust access controls including multi-factor authentication and role-based permissions, and automated tamper detection through cryptographic hashing. A purpose-built digital evidence management system implements all four by default.
About the Author
Wasif Baig
Wasif Baig is a Product Marketing Executive at VIDIZMO specializing in enterprise video streaming, digital evidence management, and AI-powered redaction. His work helps law enforcement agencies, government organizations, and enterprises understand how to manage, secure, and act on video at scale.
Jump to
You May Also Like
These Related Stories

Best Practices for Sharing Digital Evidence Securely

Why Digital Audit Trails Are Critical for Modern Evidence Management




No Comments Yet
Let us know what you think