Best Practices for Sharing Digital Evidence Securely
By Wasif Baig on April 22, 2026, ref:

Sharing digital evidence is vital for successful prosecutions, but it's a minefield of potential security pitfalls. This guide walks through how to share evidence securely with prosecutors, partner agencies, and courts while preserving the integrity of your case.
It's too easy to convict an innocent person or acquit a guilty one. A wrongful conviction is one of the gravest injustices in the criminal justice system. These errors often stem from mishandled, lost, and tampered evidence, which leads to the wrongful interpretation of crucial facts.
The National Registry of Exonerations reports that 2 to 10 percent of individuals convicted in the United States are innocent. The truth of their guilt or innocence might be hidden within the gaps of a compromised evidence trail.
Digital evidence is undeniably vital in solving criminal cases. But it is inherently fragile and susceptible to tampering and unauthorized access unless strict security measures are implemented.
Secure evidence sharing and proper evidence handling are of paramount importance. They can easily make or break the case. This was tragically illustrated by the case of David Camm, where years of legal battles were fought to overturn his conviction.
The stakes are high for digital evidence. Given the increasing use of cameras, recording devices, and electronic communication, it's not surprising that approximately 90 percent of criminal cases today involve digital evidence.
Transparency and reliability are essential for a secure evidence-sharing process. Without them, the justice system risks losing credibility. That's why it's necessary to learn the best practices for sharing digital evidence, so you can minimize concerns over tampering, unauthorized access, or misplacement.
To that end, this blog examines the critical importance of digital evidence security and provides best practices for sharing digital evidence securely among prosecutors, law enforcement professionals, and other relevant agencies.
Understanding the Importance of Secure Evidence Sharing
Digital evidence has become a cornerstone in the pursuit of justice, and its importance continues to grow rapidly. Different agencies in the criminal justice and public safety sectors, including law enforcement, prosecutors, defenders, courts, and correctional institutions, are interconnected through the act of sharing digital evidence.
Secure evidence sharing plays a crucial role in streamlining the entire justice process. It ensures evidence integrity, admissibility, and overall case success, establishing a seamless flow from the initial incident to the courtroom.
Transparency in handling and sharing evidence also ensures that all parties involved can have confidence in the process. Without this trust, investigations can be jeopardized, privacy laws may be violated, wrongful convictions may occur, and public trust will inevitably erode.
Conventional Practices of Evidence Sharing in Legal and Law Enforcement Agencies

In the past, and still today, law enforcement and legal personnel have to burn countless DVDs or transfer data to external hard drives or flash drives. It is a time-consuming and error-prone process. It's like trying to transfer a library of books by hand, one page at a time.
Once these physical copies are created, the real challenge is sharing them. Packages of data containing confidential information must be hand-delivered to the district attorney's office. This process is inefficient and poses significant risks to the digital evidence sharing process. What if something happens on the way? What if the evidence is misplaced or, worse, tampered with?
Today, law enforcement and legal professionals face immense pressure to close cases quickly, all while managing an ever-growing volume of digital evidence. From body-worn cameras and in-car videos to CCTV footage, interview recordings, and mobile phones, everything must be accounted for.
During a trial, both the prosecutor and the defense attorney share evidence through the discovery process. This process ensures that both parties have the necessary information to prepare their cases, promoting a fair trial.
The discovery process remains inefficient due to the persistence of outdated methods for sharing digital evidence. The defense and prosecution often exchange information via physical media, which must be picked up, hand-delivered, or mailed to defense counsel.
There is little to no standardization in the prosecutor's office regarding the receipt of digital evidence. Different law enforcement agencies manage and share information in various ways, such as DVDs, USB drives, hard drives, or paper reports. All of this needs to be uploaded, copied, and scanned into various systems, which slows down cases.
You can read more about this in our blog on cloud vs. physical evidence storage.
Insecure Sharing Methods to Avoid
Before looking at best practices, it's worth calling out the methods that still dominate evidence sharing but create the most risk.
Email attachments
Email was never designed for sensitive evidence. Attachments sit unencrypted on mail servers, pass through providers that don't maintain chain of custody, and can be forwarded without the sender's knowledge. Most email systems also enforce file size limits that push users toward fragmented or compressed sharing, both of which complicate authentication.
USB drives, DVDs, and external hard drives
Physical media can be lost in transit, damaged, or stolen. They lack built-in encryption, audit trails, and access controls. Once a USB drive is handed off, the sender has no way to revoke access or prove what the recipient did with the contents.
Consumer cloud links
Generic file-sharing services like Dropbox or Google Drive weren't built with CJIS, HIPAA, or GDPR compliance in mind. Links can be forwarded to unauthorized parties, access expiration is often optional, and audit logs may not meet legal evidentiary standards.
Each of these methods fails the same test: they can't prove, under legal scrutiny, who accessed the evidence, when, and what they did with it. Any evidence-sharing method that cannot answer those questions creates risk to the case.
Significant Risks of Insecure Digital Evidence Sharing

Secure evidence sharing presents challenges that differ significantly from those of securely storing it. When evidence is shared, it becomes vulnerable to significant risks like the ones outlined below.
Data Breaches and Privacy Risks
The digital realm is constantly exposed to cybersecurity threats and data breaches. The Target data breach was one of the most significant security breaches in history, with cybercriminals stealing 40 million customer credit and debit records. While not directly related to law enforcement, this case highlights the reach and consequences of a serious breach.
When digital evidence is shared without proper security measures, it becomes a prime target for hackers or malicious actors. These individuals may bypass an unprotected system easily and gain unauthorized access. Once inside, they have the potential to compromise the integrity of the case.
A data breach can expose sensitive information, including confidential investigative details and personal information about suspects, victims, and witnesses. This exposure also puts individuals at risk of identity theft, harassment, and other forms of harm.
Tampering and Alteration of Evidence
The dangers of evidence tampering are not unique to digital evidence; they also apply to traditional evidence. A recent study reported that digital evidence is more susceptible to tampering than physical evidence due to its intangible and highly volatile nature.
The study also warns that evidence tampering is so dangerous that, depending on the manipulator's intentions, the alteration can be entirely undetectable, regardless of the expertise or competence of digital forensic experts.
Once digital evidence falls into the hands of unauthorized users, they can interfere with the investigation process by altering, falsifying, or concealing the evidence. Threats can come from within the agency, such as insiders with access to the agency's system who use it to delete or replace important case files.
Comparing digital evidence with its copies to detect tampering is both time-consuming and resource-intensive. It often requires additional security infrastructure and personnel. Even then, it can be challenging to definitively determine if evidence has been tampered with.
Inadmissibility of Evidence in Court
Who collected the evidence? Who handled it? When was the evidence last accessed, and by whom? When was it transferred to another investigator for examination? What specific actions were taken with the evidence during each transfer?
These questions might seem difficult to track. But if you don't have the answers, the evidence might be worthless. These questions relate to the evidence lifecycle collectively, and their answer lies in the digital chain of custody. This is a sequential documentation of every event happening to the digital evidence.
Digital evidence can constantly be challenged in court. If the chain is broken at some point, the evidence presented will be ruled inadmissible.
The court considers the relevance, authenticity, integrity, and reliability of digital evidence in its admissibility. It carefully examines the evidence collection, storage, and transfer processes to ensure compliance with strict legal and regulatory standards. If the chain of custody is broken at any point, it means the evidence was accessed by unauthorized personnel or tampered with, making it inadmissible.
Since the evidence cannot be presented in court, it will profoundly impact the trial's dynamics and limit the scope of arguments. The burden of proof lies with the prosecution, which is responsible for proving the defendant's guilt beyond a reasonable doubt. If key evidence is dismissed, it undermines the prosecution's ability to win the case. In the worst-case scenario, it can result in the case being terminated in favor of the defense.
How to Ensure Secure Evidence Sharing: Best Practices

The risks above are preventable. The nine practices below are the baseline for any agency sharing digital evidence with prosecutors, defenders, partner agencies, or courts.
1. Protect Evidence with Encryption
Encryption is the most effective single measure to protect digital evidence. It scrambles data so it is unreadable without the correct key, and it must apply to data both at rest and in transit. Given that 7 million unencrypted records are compromised every day, encryption is non-negotiable.
The industry standard is AES-256, the encryption standard used by U.S. government agencies and approved for protecting classified information. AES-256 alone is not enough, though. It is only as strong as the security infrastructure around it, so treat it as one layer of defense in depth.
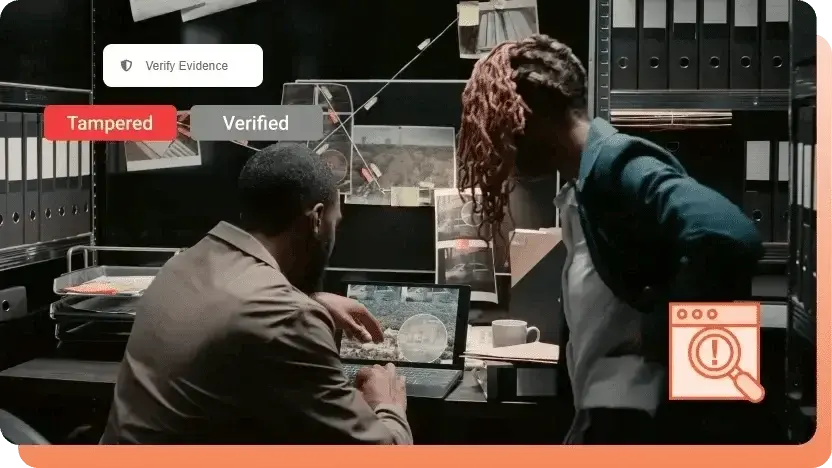
2. Verify Integrity with Tamper Detection
Any alteration to a shared evidence file can render it inadmissible. Tamper detection prevents that by assigning each file a unique cryptographic hash value at upload. If the file is altered afterwards, the hash changes, flagging the tampering immediately.
Manual verification is impractical at modern evidence volumes. Automated hash verification on every access is the only scalable way to prove a file is unchanged.
3. Restrict Access to Authorized Users Only
Digital evidence security collapses the moment files reach the wrong hands. Role-Based Access Control (RBAC) solves this by assigning permissions by role: a chief of police sees the full case file, while a patrol officer sees only what is relevant to their work.
Pair RBAC with automatic session timeouts so unattended devices don't become an access gap.
4. Maintain a Chain of Custody
Evidence is only admissible if you can prove who accessed it, when, and what they did. A complete chain of custody captures every action on every file, including the user, timestamp, and activity performed (viewed, copied, downloaded, modified).
Chain of custody works in combination with RBAC, tokenized links, and encryption. Together, these create the unbroken audit trail courts require.
5. Use Limited, Time-Bound Sharing Links
Open access to evidence files is an open door to tampering. Share through links that expire after a set period, require a password, and cap the number of views.
Different recipients should get different links. A defense attorney may need two-day access to a single clip, while a co-investigator may need longer access to the full case file. Issuing separate links lets you tailor permissions without duplicating the underlying evidence.
6. Limit Access by Geographic Region
Location restrictions add another layer by limiting who can access evidence based on where they are signing in from. This helps defend against credential theft, since stolen login details cannot be used from outside the authorized region.
7. Use Separate Portals for Separate Departments
Not every department in an agency, and not every agency in a task force, needs access to the same evidence pool. Separate portals segregate evidence by team or organization, so a user in one department cannot see what belongs to another without explicit authorization. For multi-agency investigations, this model enables fast collaboration without flattening permissions. See our guide on multi-agency evidence sharing for more.
8. Use AI-Powered Redaction for PII
Digital evidence often contains PII that cannot be shared unredacted: Social Security numbers, phone numbers, names, addresses, faces, license plates. Failing to redact this data can expose victims and witnesses, breach privacy regulations, and in some cases render the evidence inadmissible.
Manual redaction is accurate but slow. An hour of body-worn camera footage can take several hours to redact frame by frame. AI-powered redaction solves the volume problem, automatically detecting and obscuring sensitive information across video, audio, images, and documents. The strongest approach pairs AI detection with a human reviewer who verifies the output before release.
9. Use a Digital Evidence Management System
The practices above are powerful individually, but they only work when they operate together. Encryption alone does not solve access control. Access control alone does not prove chain of custody. A Digital Evidence Management System (DEMS) unifies all of these controls in one platform, which is why single-purpose tools consistently fall short of what evidence workflows demand.
Compliance Requirements When Sharing Digital Evidence
Beyond the practices above, any organization sharing digital evidence must meet the compliance standards that apply to its sector and jurisdiction. Three frameworks are most commonly referenced in evidence workflows:
CJIS (Criminal Justice Information Services). The FBI's CJIS Security Policy governs how criminal justice information is stored, accessed, and transmitted by law enforcement agencies in the United States. It includes requirements for encryption, user authentication, audit logging, and physical security. Any evidence-sharing platform used by U.S. law enforcement must be built to meet CJIS Security Policy requirements.
HIPAA (Health Insurance Portability and Accountability Act). When digital evidence contains protected health information, such as medical records, clinical images, or recordings from healthcare settings, HIPAA applies. HIPAA requires administrative, physical, and technical safeguards around the sharing of protected health information, including access controls, audit trails, and breach notification.
GDPR (General Data Protection Regulation). For cases involving subjects in the European Union, or evidence shared with EU-based agencies, GDPR applies. GDPR requires a lawful basis for processing personal data, strong access controls, data minimization, and the ability to demonstrate compliance through documentation.
Other frameworks may also apply depending on the agency and case type, including the Freedom of Information Act for U.S. government records, state-level public records acts, and sector-specific regulations for financial or corporate evidence. A digital evidence management system should make it straightforward to demonstrate compliance with the frameworks relevant to your workflow.
VIDIZMO Digital Evidence Management System for Secure Evidence Sharing
For law enforcement agencies sharing evidence with prosecutors, courts, and partner agencies, VIDIZMO Digital Evidence Management System provides a centralized platform to ingest, store, manage, analyze, and share digital evidence.
VIDIZMO Digital Evidence Management System supports the practices covered in this guide:
- Ingest digital evidence from multiple sources, including dashcams, body-worn cameras, interview rooms, and mobile uploads
- Protect evidence files with AES-256 end-to-end encryption, at rest and in transit
- Detect tampering using cryptographic hashing to verify file integrity at every access
- Maintain a complete chain of custody report for each evidence file, logged automatically
- Control access with Role-Based Access Control at the case and user level
- Restrict access by IP address and geographic region
- Share evidence externally via tokenized links with expiration dates, view limits, and password protection
- Automatically redact faces, license plates, weapons, vehicles, and other sensitive information using AI
- Built to meet CJIS, HIPAA, and GDPR requirements for evidence handling
If you are evaluating solutions for secure evidence sharing, you can try VIDIZMO DEMS and see how it handles your agency's evidence workflow.
People Also Ask
Digital evidence refers to data stored or transmitted in digital form that can support investigations or legal proceedings. It plays a pivotal role in solving crimes, proving innocence or guilt, and ensuring justice, especially in cases involving video footage, digital communications, or metadata.
Secure evidence sharing ensures the integrity, authenticity, and admissibility of digital evidence in court. It helps prevent unauthorized access, tampering, or data loss, which could otherwise lead to wrongful convictions or dismissed charges.
Insecure digital evidence sharing exposes files to risks like data breaches, tampering, unauthorized access, and inadmissibility in court. These vulnerabilities can compromise investigations, infringe on victim and witness privacy, and affect legal outcomes.
Encryption converts data into unreadable code, making it inaccessible to unauthorized users. End-to-end encryption, especially AES-256, ensures that files remain secure both at rest and in transit.
Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aenean commodo ligula eget dolor. Aenean massa. Cum sociis natoque penatibus et magnis dis parturient montes, nascetur ridiculus mus. Donec quam felis, ultricies nec, pellentesque eu, pretium quis, sem. Nulla consequat massa quis enim. Donec pede justo, fringilla vel, aliquet nec, vulputate eget, arcu. In enim justo, rhoncus ut, imperdiet a, venenatis vitae, justo. Nullam dictum felis eu pede mollis pretium. Integer tincidunt. Cras dapibus. Vivamus elementum semper nisi.
The three most commonly referenced standards are CJIS (for U.S. law enforcement), HIPAA (for protected health information), and GDPR (for personal data of EU subjects). Other frameworks such as FOIA and state-level public records acts may also apply depending on the agency and case type.
A Digital Evidence Management System is a secure platform that enables law enforcement and legal teams to ingest, manage, analyze, and share digital evidence. It incorporates encryption, access control, chain of custody, and tamper detection to maintain the integrity of evidence.
Tamper detection uses cryptographic hash values to check whether digital evidence has been altered. If the hash value changes, it indicates tampering, helping maintain the evidence's credibility and compliance with legal standards.
The chain of custody is a detailed log of all actions taken on a piece of digital evidence. It tracks who accessed it, when, and what changes were made. A strong chain of custody ensures evidence remains untampered and admissible in court.
Expiring tokenized links are shareable URLs that grant access to a specific evidence file for a limited time and under controlled conditions. They can enforce password protection, view limits, and automatic expiration, which prevents indefinite access and ensures that revoked permissions take effect immediately.
Granular access control limits user permissions based on roles, allowing only authorized personnel to view or manage digital evidence. This prevents unnecessary exposure and minimizes internal and external security threats.
Physical storage devices are prone to loss, damage, and unauthorized access. They lack encryption, audit trails, and tamper detection, making them less secure than digital systems for sharing sensitive evidence.
Law enforcement agencies can securely share evidence with prosecutors using a DEMS that supports encrypted links, role-based access control, tamper detection, time-bound access, and separate portals for different agencies.
About the Author
Wasif Baig
Wasif Baig is a Product Marketing Executive at VIDIZMO specializing in enterprise video streaming, digital evidence management, and AI-powered redaction. His work helps law enforcement agencies, government organizations, and enterprises understand how to manage, secure, and act on video at scale.
Jump to
You May Also Like
These Related Stories

How Digital Evidence Management Systems Solve Physical Storage Issues?
How to Prevent Digital Evidence Tampering and Ensure Integrity




No Comments Yet
Let us know what you think