Police Evidence Management: 10 Features That Protect Cases & Save Time
By Sarim Suleman on April 21, 2026, ref:
Police evidence management is the process of ingesting, storing, tracking, analyzing, and sharing digital evidence within a law enforcement agency. It covers body-worn camera footage, in-car video, surveillance recordings, 911 audio, and photos collected at crime scenes. When done well, every piece of evidence remains intact, attributable, and admissible from the moment of collection through courtroom presentation.
The volume of digital evidence is growing fast. A Police Executive Research Forum (PERF) report found that most agencies now manage terabytes of video annually, yet many still rely on physical media like DVDs, USB drives, and standalone hard drives. That gap between evidence volume and management capacity leads to lost files, broken chains of custody, and dismissed cases.
This guide breaks down the 10 features that matter most when evaluating law enforcement evidence management software. Whether you're replacing a legacy system or building a centralized evidence repository for the first time, these capabilities determine whether your evidence holds up in court, meets compliance mandates, and helps investigators close cases faster.
Key Takeaways
- Chain of custody and tamper detection aren't optional. They're the foundation of court-admissible evidence handling.
- CJIS compliance is a baseline requirement, but agencies should also evaluate FedRAMP, FIPS 140-2, and state-specific mandates.
- AI-powered search and transcription can cut manual evidence review time from hours to minutes across large case files.
- Deployment flexibility (cloud, on-premises, hybrid) matters because data sovereignty requirements vary by jurisdiction.
- Multi-agency sharing with role-based access controls prevents unauthorized exposure while enabling collaboration with prosecutors and defense counsel.
What Is Law Enforcement Evidence Management Software?
Law enforcement evidence management software centralizes the intake, storage, processing, and sharing of digital evidence for police departments and public safety organizations. It replaces fragmented workflows involving physical media, network file shares, and standalone storage devices with a single, auditable repository.
A good system does more than store files. It maintains an unbroken chain of custody from the moment evidence is uploaded. It enforces access controls so only authorized personnel can view, download, or share specific items. And it provides search capabilities that let investigators locate a specific clip from thousands of hours of footage in seconds.
The difference between a file storage tool and a true evidence management platform comes down to three things: integrity verification (proving evidence hasn't been altered), compliance enforcement (meeting CJIS Security Policy and other mandates automatically), and lifecycle management (retention, legal hold, and disposition according to policy).
Why Do Police Departments Need Dedicated Evidence Management Systems?
General-purpose file storage doesn't meet the legal and operational requirements of evidence handling. A police department can't store body camera footage on a shared drive and expect it to hold up in court. Defense attorneys will challenge the chain of custody, and without tamper detection and audit logging, there's no way to prove the file wasn't altered.
The operational burden is significant, too. Agencies handling thousands of cases simultaneously need automated workflows for ingestion, categorization, and retention. Manual processes break down at scale. Officers end up burning DVDs or transferring USB drives instead of investigating cases.
Then there's the compliance dimension. The CJIS Security Policy mandates specific encryption standards, access controls, and audit logging for any system that handles criminal justice information (CJI). State laws like California's AB-748 require body-worn camera footage to be released within 45 days of certain incidents. A dedicated evidence management system enforces these rules automatically instead of relying on manual compliance.
How Does Chain of Custody Tracking Protect Case Outcomes?
Chain of custody is the documented record of every person who accessed, modified, transferred, or viewed a piece of evidence, along with the exact time and action taken. Without it, evidence can be challenged as unreliable or inadmissible under the Federal Rules of Evidence.
A single gap in the custody record can unravel months of investigative work. An effective evidence management system logs every interaction automatically: the IP address, username, timestamp, and specific action (view, download, share, annotate) for every event. These logs should be stored in write-once, read-many (WORM) storage so they can't be edited or deleted after the fact.
What to look for in chain of custody features
- Automatic logging of all evidence interactions without manual entry
- Hash-based integrity verification (SHA-256 is the current standard) that detects any file modification
- Exportable chain of custody reports in PDF and CSV formats for court proceedings
- WORM-enabled audit log storage that prevents tampering with the logs themselves
- One-click tamper detection that compares current file hashes against originals
For a deeper dive into maintaining evidence integrity, see our guide on 10 chain of custody best practices.
What Role Does CJIS Compliance Play in Evidence Management?
Any system that stores, processes, or transmits criminal justice information must comply with the CJIS Security Policy. This isn't optional. It's a federal requirement covering encryption standards, personnel security, access controls, and audit logging. Agencies that fail to comply risk losing access to FBI databases and face potential legal liability.
CJIS compliance requires AES-256 encryption for data at rest and TLS 1.2 (minimum) for data in transit. It mandates multi-factor authentication (MFA) for all users accessing the system remotely. It requires background checks for personnel with access to criminal justice information. And it demands comprehensive audit logging that can be reviewed on demand.
For a detailed walkthrough of how these controls apply to digital evidence systems specifically, read our article on CJIS compliance in digital evidence management.
How Does Multi-Source Evidence Ingestion Work?
Modern police departments collect evidence from a wide range of sources: body-worn cameras, in-car dash cameras, interview room recordings, CCTV systems, drones, cell phone extractions, 911 audio, and citizen-submitted media. An evidence management system needs to handle all of these from a single interface.
The key capabilities to evaluate are format support (look for systems that handle 200+ file types natively), automated ingestion (watch folders that detect new files and import them automatically), and bulk upload (for transferring large batches from camera docking stations or network drives). Mobile upload from officer devices in the field is increasingly important as well.
Vendor-agnostic ingestion eliminates hardware lock-in
Some evidence platforms only work with specific camera manufacturers. That creates vendor lock-in and forces agencies to replace working equipment to adopt a new management system. The better approach is a platform that ingests from any source, regardless of manufacturer. This way, agencies choose cameras based on operational needs, not software compatibility. For a comparison of how different platforms handle this, see our evidence storage and retrieval software guide.
Why Does Deployment Flexibility Matter for Law Enforcement?
Not every agency can use cloud storage for evidence. Some jurisdictions have data sovereignty laws that require evidence to remain within state or county boundaries. Federal agencies handling classified material need air-gapped environments. Other departments want the cost savings and scalability of cloud but need a transition path from existing on-premises infrastructure.
The right evidence management platform offers multiple deployment options: cloud (both commercial and government), on-premises, private cloud, and hybrid configurations. This flexibility lets an agency start with one model and migrate as requirements change, without switching vendors or re-ingesting evidence.
For agencies evaluating cloud options, check whether the vendor supports FedRAMP-authorized environments and government-specific cloud regions. These provide the security controls needed for CJIS-compliant cloud evidence storage.
How Can AI-Powered Search Accelerate Investigations?
Investigators working major cases often face hundreds or thousands of hours of video evidence. Reviewing all of that manually isn't realistic. AI-powered search lets investigators query evidence using natural language, metadata, transcripts, and visual attributes to find relevant clips in seconds.
The most impactful AI capabilities for law enforcement evidence management include:
- Automatic transcription that converts audio and video speech to searchable text, enabling keyword searches across all recordings in a case
- Object detection that identifies faces, vehicles, license plates, weapons, and other objects across video footage
- Speaker diarization that distinguishes between speakers in interview and interrogation recordings
- Automatic summarization that generates concise summaries of lengthy recordings so investigators can triage faster
- Geospatial mapping that plots evidence on maps using GPS metadata from body cameras and drones
These tools don't replace human judgment. They help investigators focus their time on the evidence that matters most, cutting review time on large case files from days to hours. Learn more about how these capabilities work together in our deep dive on AI-powered digital evidence management.
What Security Controls Should Evidence Management Software Include?
Evidence management systems store some of the most sensitive data a government agency handles. The security model needs to go beyond basic username and password authentication. At minimum, look for role-based access control (RBAC), single sign-on (SSO) integration, multi-factor authentication, and IP or domain-based access restrictions.
How Role-Based Access Control Works in Practice
Different users need different levels of access. A patrol officer should be able to upload evidence and view their own cases. A detective needs broader search and review capabilities. An evidence custodian needs administrative control over retention and disposition. A prosecutor needs read-only access to shared case files. Internal affairs investigators need a completely separate, segregated workspace.
The best systems support granular roles (not just "admin" and "user") along with per-portal or per-case access policies. This prevents unauthorized cross-case visibility and protects sensitive investigations from internal exposure.
Encryption and Zero-Trust Architecture
Evidence should be encrypted at rest (AES-256) and in transit (TLS 1.2 or higher). Encryption key management should follow industry standards, with regular key rotation. Staff access to the platform infrastructure should follow zero-standing-access principles, meaning vendor employees don't have persistent access to customer data. For more on how digital evidence preservation supports these security requirements, see our dedicated guide.
How Does Multi-Agency Evidence Sharing Improve Collaboration?
Investigations frequently cross jurisdictional boundaries. A local police department may need to share body camera footage with a county prosecutor, state investigators, or federal agencies like the FBI. Without a structured sharing mechanism, agencies resort to burning DVDs, uploading to insecure file-sharing services, or hand-delivering hard drives.
Effective evidence sharing requires two things: security and simplicity. The sharing mechanism should enforce access controls (who can view, download, or forward), time limits (links that expire after a set period), and audit trails (recording exactly who accessed shared evidence and when).
Portal-Based Architecture for Multi-Stakeholder Access
A portal-based architecture creates separate, secured workspaces for different stakeholders within a single platform. A law enforcement portal handles active investigations. A prosecution portal gives attorneys access to relevant case evidence. A community portal lets citizens submit tips and footage securely. An internal affairs portal provides segregated access for conduct investigations. Each portal has its own security policies, user roles, and audit trails.
This model eliminates the need for multiple systems while maintaining strict evidence segregation between stakeholders.
How Does Multi-Agency Evidence Sharing Improve Collaboration?
Investigations frequently cross jurisdictional boundaries. A local police department may need to share body camera footage with a county prosecutor, state investigators, or federal agencies like the FBI. Without a structured sharing mechanism, agencies resort to burning DVDs, uploading to insecure file-sharing services, or hand-delivering hard drives.
Effective evidence sharing requires two things: security and simplicity. The sharing mechanism should enforce access controls (who can view, download, or forward), time limits (links that expire after a set period), and audit trails (recording exactly who accessed shared evidence and when).
Portal-based architecture for multi-stakeholder access
A portal-based architecture creates separate, secured workspaces for different stakeholders within a single platform. A law enforcement portal handles active investigations. A prosecution portal gives attorneys access to relevant case evidence. A community portal lets citizens submit tips and footage securely. An internal affairs portal provides segregated access for conduct investigations. Each portal has its own security policies, user roles, and audit trails.
This model eliminates the need for multiple systems while maintaining strict evidence segregation between stakeholders.
What Evidence Redaction Capabilities Are Required for FOIA Compliance?
Public records requests under FOIA and state open records laws require agencies to release evidence while protecting personally identifiable information (PII), ongoing investigation details, and other exempt content. Manual redaction of video is extremely time-consuming. A single hour of body-cam footage can take eight or more hours to redact frame by frame, pulling officers and staff away from higher-priority work.
Look for automated redaction capabilities that include automatic face detection and blurring, license plate detection, spoken PII redaction (names, addresses, Social Security numbers), and document redaction for PDFs and images. The system should support multiple redaction styles (blur, pixelate, black box) and allow reviewers to apply redaction layers by exemption category so different versions can be exported for different requesters.
Agencies subject to California's AB-748 need to release critical incident footage within 45 days. Without automated redaction tools, meeting that deadline is nearly impossible for departments handling high volumes of requests. Learn more about why this matters in our blog on digital evidence management after body-worn camera adoption.
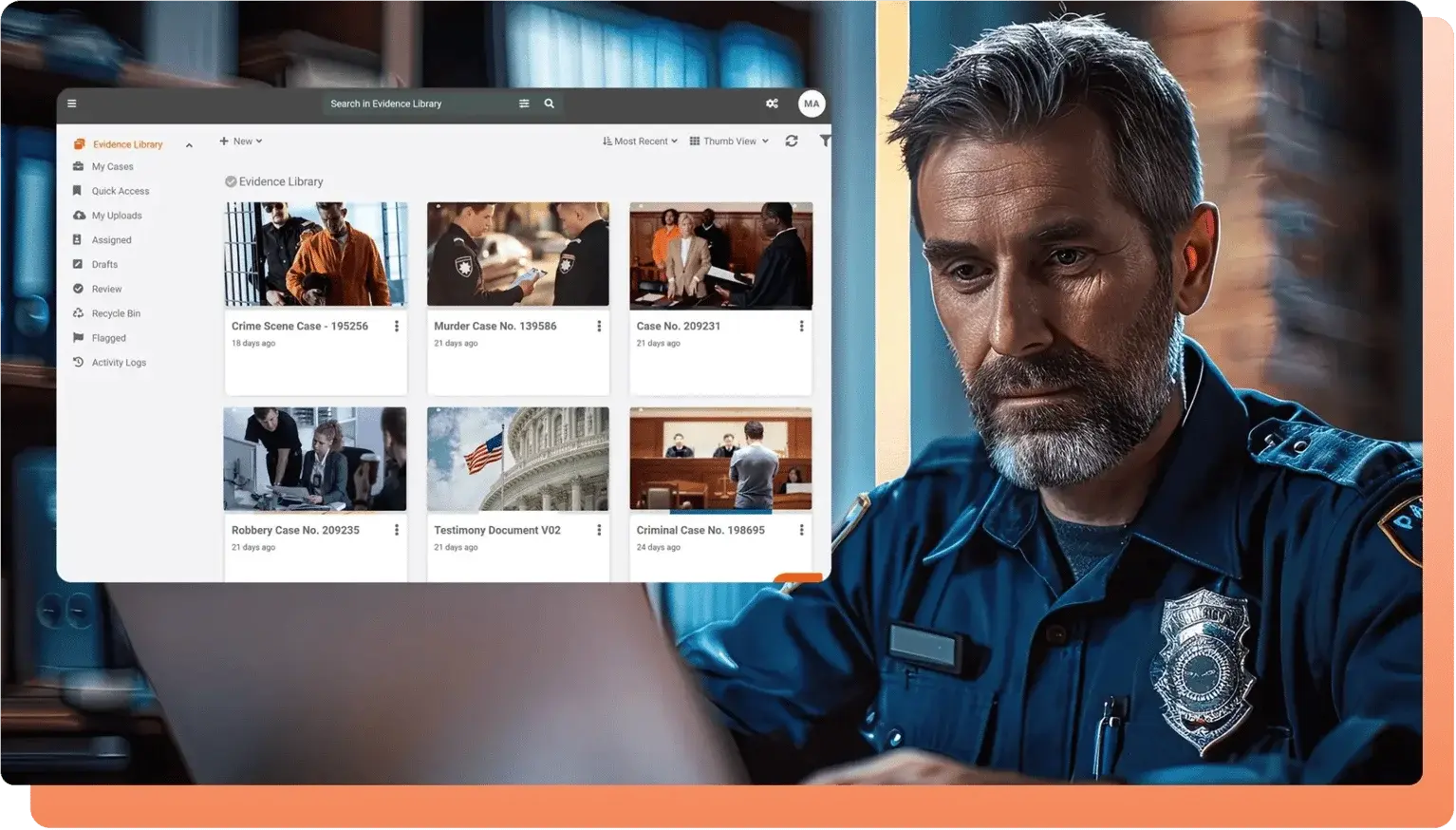
How VIDIZMO DEMS Brings These Features Together
Law enforcement agencies require a secure, scalable, and efficient solution to manage digital evidence, ensuring seamless collaboration across departments. VIDIZMO Digital Evidence Management System (DEMS), a leading law enforcement evidence management software, provides a centralized and highly secure platform that enables officers, investigators, and legal teams to store, access, and share digital evidence with advanced security controls.
With features like Partner Agency Integration, AI-powered search, tokenized URL sharing, and end-to-end encryption, VIDIZMO DEMS ensures that evidence is shared in real time while maintaining compliance with chain of custody requirements and legal standards.
Unlike traditional evidence management methods, VIDIZMO DEMS integrates seamlessly with Records Management Systems (RMS), Computer-Aided Dispatch (CAD), and offers API-based, customized integration, creating a seamless workflow that enhances operational efficiency.
Also, with granular access controls, automated tamper detection, and selective metadata sharing, agencies can ensure data integrity, prevent unauthorized access, and maintain transparent audit trails. By adopting VIDIZMO DEMS, law enforcement agencies can streamline interdepartmental communication, enhance investigative efficiency, and ensure secure collaboration, making it an indispensable tool for modern policing.
Ready to see how a centralized evidence platform works in practice? Contact us to evaluate the platform with your own evidence workflows.
People Also Ask
It's a platform that centralizes intake, storage, chain of custody tracking, AI-powered analysis, and sharing of digital evidence. It replaces manual processes like DVD burning and USB transfers with automated, auditable workflows.
The system automatically logs every interaction, including who accessed a file, what they did, their IP address, and the exact timestamp. Logs are stored in WORM (write-once, read-many) storage to prevent tampering, and SHA-256 hashing lets investigators verify file integrity with one click.
CJIS Security Policy compliance is the baseline: AES-256 encryption, MFA, and audit logging. Federal agencies should also look for FedRAMP High and FIPS 140-2 validation. Depending on jurisdiction, HIPAA, FOIA, NARA, and state mandates like California AB-748 may also apply.
Automatic transcription, object detection, and natural-language search let investigators find specific moments across thousands of hours of footage in seconds. AI also speeds up FOIA redaction by detecting faces, license plates, and spoken PII automatically. VIDIZMO DEMS offers transcription in 82 languages and a CaseBot feature for plain-language evidence queries.
General storage tools (network drives, SharePoint, cloud storage) lack chain of custody tracking, tamper detection, CJIS enforcement, and role-based access controls. Without a verifiable audit trail, evidence stored on these platforms is vulnerable to admissibility challenges in court.
Yes. Vendor-agnostic platforms accept footage from any manufacturer, including Axon, Motorola, Panasonic, and others, preventing hardware lock-in. Look for automated watch-folder ingestion that imports files from docking stations regardless of brand.
About the Author
Sarim Suleman
Sarim Suleman is a Product Marketing Executive at VIDIZMO with deep expertise in enterprise video platforms and digital evidence management. He focuses on helping government agencies and large-scale organizations understand how modern video and AI technology can transform their evidence workflows and operational efficiency.
Jump to
You May Also Like
These Related Stories

The Real Cost of Burning DVDs for Evidence at Small Police Departments
Evidence Management System: Core Features, and How to Choose One





No Comments Yet
Let us know what you think