
Attorney-Client Privilege and Digital Evidence: Protecting Client Data
Most digital evidence management platforms are built for law enforcement. They solve for chain-of-cu …
Evidence Disposition Best Practices: When and How to Destroy Digital Evidence
Every piece of digital evidence has an expiration date. Yet for most law enforcement agencies, digit …

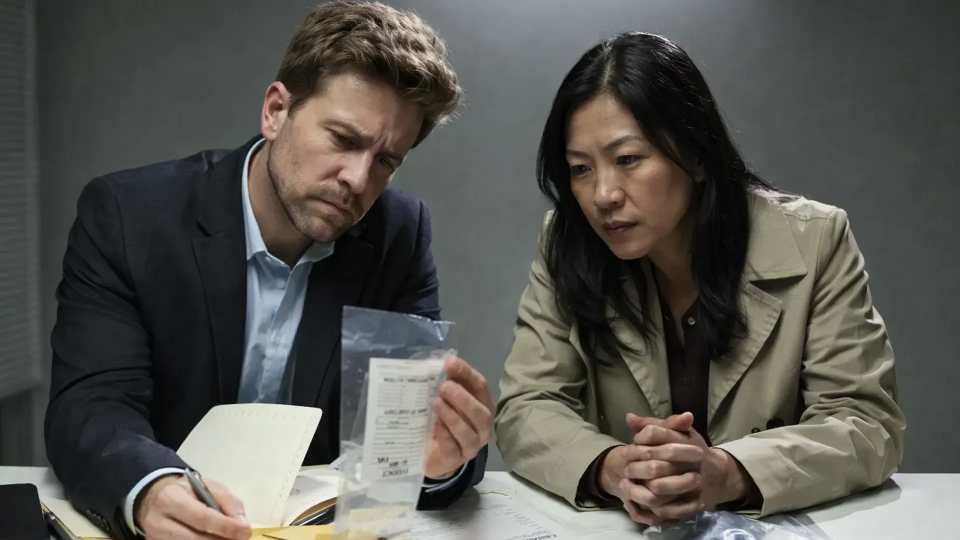
How Public Safety Agencies Manage Digital Evidence After Incidents
Public safety incidents do not end when the situation is controlled. They continue through investiga …
.webp)
Digital Audit Trails vs Audit Logs: What’s the Difference and Why It Matters
Most organizations can confirm that activity is being logged somewhere in their systems. What many c …

Ensuring Your Evidence Disclosure Process Meets FOIA Standards
FOIA requests rarely fail because agencies refuse to disclose evidence. They fail because the FOIA e …

Why Retention and Deletion Are the Riskiest Stages of Digital Evidence
Retention and deletion are often treated as routine administrative steps in digital evidence managem …

Understanding CJIS Compliance in Digital Evidence Management
Most justice agencies have a CJIS security addendum on file and a policy manual that looks solid dur …

Long-Term Evidence Storage for Secure and Compliant Evidence Retention
Evidence does not become less important with time. In many cases, its importance increases. Organiza …

Ensuring Robust Governance Across the Digital Evidence Lifecycle
Digital evidence plays a central role in investigations, litigation, compliance reviews, and interna …

